Mission data.
Verifiably erased.
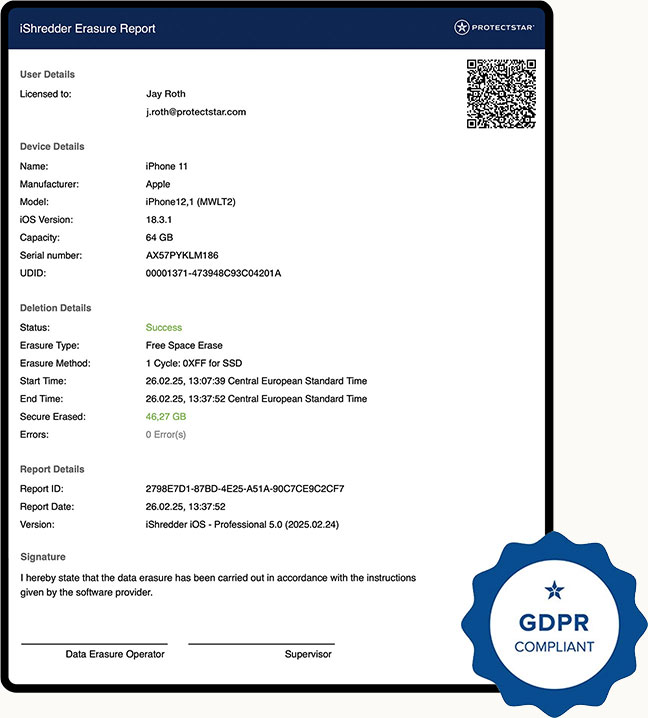
Offline sanitization aligned with NIST SP 800-88r2 and IEEE 2883 — for drone storage, controllers, and mobile mission platforms. Includes a digitally signable erasure report for chain-of-custody evidence, audits, and procurement.
The Scenario
A drone is intercepted.
The risk starts long before that.
Mission storage media, controllers, returned devices, test systems, and decommissioned media can all contain video material, telemetry, route data, and black-box logs that may be recoverable with suitable forensic tools. iShredder™ Defense sanitizes this data before reuse, maintenance, return, or decommissioning according to recognized standards, making recovery impractical within a defined forensic-effort model.
Mission videos, GPS telemetry, black-box logs — structured and stored on the device. With standard recovery tools, this type of data can potentially be reconstructed.
The Product
One tool. For every platform.
iShredder™ Defense works fully offline and selects the strongest available sanitization method for each medium — from NVMe Sanitize and ATA Secure Erase to Crypto Erase and verified overwrite. Every operation ends with a digitally signable erasure report for chain-of-custody documentation.
In development · Evaluation units availableFully offline
No cloud connection, no external servers. Works in secure depots and in the field — including air-gapped environments.
Audit-ready
Signable erasure reports with method, timestamps, device IDs, and LBA coverage for an unbroken chain of custody.
Cross-platform
Windows, macOS, iOS, and Android. For depot workstations and controller tablets — one workflow, consistent reports.
Workflow
Five steps. One report.
- 01 Identify
medium - 02 Select
profile - 03 Execute
method - 04 Perform
verification - 05 Sign
report
Media Support Matrix
Not every medium supports every method.
iShredder™ Defense selects the strongest available sanitization method based on medium, interface, security profile, and audit requirements. The matrix shows the primary methods by media type.
Note on flash media: With storage that uses overprovisioning and wear leveling (SSDs, eMMC, SD), overwrite alone cannot guarantee complete sanitization. For these media types, device- and controller-specific sanitize commands are preferred (NVMe Sanitize, ATA Secure Erase, Crypto Erase) — aligned with NIST SP 800-88r2 and IEEE 2883. TRIM/Discard is used only as a supporting command and is not sufficient as standalone proof of sanitization.
The Evidence
Recoverable before. Verifiably sanitized after.
Example representation of a sanitization workflow on an NVMe mission-storage device. Actual results depend on the medium, controller, selected profile, and verification method.
LBA 0x00001000: 00 00 00 00 · 00 00 00 00
LBA 0x00002000: 00 00 00 00 · 00 00 00 00
... addressable ranges · verified
Chain of Custody
Not just erased.
Proven sanitized.
Every sanitization operation with iShredder™ Defense ends with a digitally signable erasure report. All relevant parameters are documented in both machine-readable and human-readable form — for audits, procurement reports, and chain-of-custody proof.
In Comparison
Why iShredder™ Defense — and not the alternatives?
erasure tools
drone tools
Defense
NVMe Sanitize · ATA Secure Erase · eMMC · SD-ERASE
Frequently Asked Questions
What procurement teams ask first.
Yes — and it was deliberately designed that way. iShredder™ Defense does not require an internet connection or any cloud component. Not for sanitization itself, and not for verification or reporting.
Specifically, this means: no telemetry, no automatic background updates, no call-home functionality, and no analytics. All processes run exclusively locally.
License activation is performed offline via a signed activation file that can be transferred into the isolated environment using secure transfer procedures. Updates are provided as signed offline packages and deployed manually — optionally with staging in a separate test zone before production rollout. This enables iShredder™ Defense to meet the requirements of classified deployment environments in line with BSI SÜG practices and applicable NATO requirements.
iShredder™ Defense logs every step of the sanitization process in an encrypted, persistent state file. If an interruption occurs — due to power loss, hardware failure, or user cancellation — the exact progress is detected at the next start.
Depending on the method, the process can either resume from the interrupted LBA range or — for hardware-level purge commands — query the internal status of the storage device. NVMe Sanitize and ATA Secure Erase are interruption-resistant on the device side and automatically continue to completion when power is restored.
Critical for audits: the erasure report explicitly documents every interruption — with timestamp, cause, and the state of the storage medium before and after the event. This prevents the loss of audit information and keeps the chain of custody complete even during incidents.
Each erasure report is protected with an X.509 signature based on the individual certificate of the respective iShredder™ Defense installation. The signature covers method, timestamps, device IDs, LBA coverage, and all other parameters — making subsequent tampering cryptographically detectable.
In addition, a SHA-256 hash of the entire report is generated and stored in a separate audit log, optionally also via a central audit-server component. The signatures are PAdES-compliant as advanced electronic signatures under the eIDAS Regulation.
For operations with the highest evidentiary requirements, reports can also be protected with a qualified electronic signature (QES) and a qualified timestamp from a qualified trust service provider. The specific integration is agreed with the customer as part of the pilot program.
iShredder™ Defense is not an ITAR-controlled product — it is commercial data erasure software, not a defense article under the U.S. Munitions List.
However, the product is subject to the U.S. Export Administration Regulations (EAR) because it contains cryptographic components. The specific ECCN classification, applicable license exceptions, end-use and end-user review, and reporting obligations are provided on a product- and release-specific basis as part of qualified evaluations.
Protectstar supports the entire end-user certification process, screens applicable sanctions lists, and provides the documentation required for export.
Yes. For government agencies, armed forces, and enterprise customers, Protectstar offers notarized source-code escrow through independent trustees in Germany and/or the United States.
Deposited materials include the full source code of the release-ready version, build instructions and build toolchain (documented for reproducibility), the list of dependencies, public verification certificates, and release documentation. Private production signing keys are expressly excluded from escrow.
Release conditions are agreed individually in the license agreement. Typical triggers include insolvency, long-term discontinuation of product maintenance, or failure to provide contractually guaranteed security updates. Scope, update cycles, and audit rights are defined for enterprise customers by SLA.
Development takes place at Protectstar-owned sites in Germany and the United States. Commits are signed and pass through a code review process.
For Defense releases, reproducible builds (deterministic builds) on isolated build machines are planned. Each release is delivered with a Software Bill of Materials (SBOM) in CycloneDX format, listing third-party libraries including versions and licenses.
Binaries are signed with Authenticode (Windows) or Developer ID (macOS); release artifacts are additionally signed with PGP. Security-relevant third-party libraries are monitored via CVE monitoring (NIST NVD, GitHub Security Advisories). Specific patch SLAs are agreed at the enterprise level in the support contract.
Yes. iShredder™ Defense provides two integration layers: a command-line interface (CLI) for script-based automation in depot processes and — planned for Defense releases — a REST API for integration into centralized management systems.
Erasure reports can be exported in JSON or CEF format and connected to common SIEM systems, including Splunk, Elastic Stack, IBM QRadar, and Microsoft Sentinel. For MDM platforms, including Microsoft Intune, Jamf Pro, and VMware Workspace ONE, connectors are provided as part of the pilot program.
Each event is also logged locally to maintain a complete evidence chain even if central infrastructure fails. The specific integration — including field mapping, authentication method, and alerting rules — is configured and documented together with the customer.
Protectstar Inc. is a U.S. company headquartered in Florida, USA. The software is developed primarily in the United States and Germany — both “Designated Countries” under the Trade Agreements Act (TAA).
TAA compliance, including “substantial transformation” documentation, is confirmed on a product- and release-specific basis and can be placed in procurement records as supporting evidence.
Procurement documentation for relevant U.S. federal and NATO procurement channels is provided as part of qualified evaluations. For specific requirements, such as a Buy American Act waiver, we can support the application process on a case-by-case basis.
Evidence, Standards & References
Three layers. Clearly separated.
Product security, sanitization standards, and procurement evidence — each layer with its own evidence, without mixing scopes.
Product & App Security
Validated at product and build level
- DEKRA MASA L1 Validated for iShredder Android (Mobile App Security Assessment, Baseline)
- AV-TEST Multiple portfolio certifications (product-specific)
- Signed Builds Authenticode · Developer ID · PGP · reproducible builds
- SBOM Software Bill of Materials in CycloneDX format for each release
Sanitization Standards
Aligned with relevant methods
- NIST SP 800-88r2 Current baseline (September 2025) — Clear / Purge / Destroy
- IEEE 2883 Standard for Sanitizing Storage
- BSI CON.6 IT-Grundschutz module for deletion and destruction
- NSA/CSS 9-12 Destroy workflow using EPL-listed devices
- Legacy DoD 5220.22-M Profiles available where existing policies require them
Procurement & Audit
Verifiable, documented, auditable
- Signed Reports X.509 · PAdES · optional QES/TSA via qualified trust service providers
- Export Formats PDF/A-3 · JSON · XML for SIEM and archives
- Timestamping Optional TSA under RFC 3161 (qualified timestamp service)
- GDPR Support Supports documentation and proof obligations for erasure processes
- Source-Code Escrow Notarized deposit · for enterprise and government customers
Individual certifications refer to specific products and versions within the Protectstar portfolio. Exact scopes of validity are documented on a product-specific basis as part of the pilot program. No endorsement by government agencies is implied.
Early Access · Pilot Program 2026/2027
Evaluation units first.
Then broader rollout.
We prioritize government agencies, armed forces, and defense contractors for the pilot program. We respond after qualification.
 English
English Deutsch
Deutsch Español
Español Français
Français Italiano
Italiano Português
Português Русский
Русский العربية
العربية हिन्दी
हिन्दी 日本語
日本語 简体中文
简体中文

